What is Carding
Carding (also known as credit card stuffing and card verification) is a web security threat in which attackers use multiple, parallel attempts to authorize stolen credit card credentials. Carding is performed by bots, software used to perform automated operations over the Internet. The objective of carding is to identify which card numbers or details can be used to perform purchases.
Besides the damage caused to card owners, a carding attack can negatively affect businesses whose websites are used to authorize stolen credit cards. Carding typically results in chargebacks – these are disputed transactions that result in a merchant reversing the transaction and refunding the purchaser’s money.
Chargebacks can happen for legitimate reasons (for example an erroneous purchase or a clerical error), but are very often the result of fraud techniques like carding. Every chargeback hurts a business’s reputation with credit card processors. Carding executed against a website can lead to poor merchant history and chargeback penalties.
Inside a Carding Forum
A carding forum or carding website is an illegal site used to share stolen credit card data, and discuss techniques for obtaining credit card data, validating it and using it for criminal activity.
These forums are used by individuals who want to use stolen card information to illicitly purchase goods, or by criminal groups who seek to purchase credit card details in bulk to sell them on the dark web.
Carding forums are often hidden using TOR routing, and payments made for stolen credit card data are performed using cryptocurrency to avoid tracking by the authorities. Forum users typically hide their identities.
Forums are a source of credit card data for carding, and can also be used to share the results of carding – for example to sell success credit cards to other criminals.
How a Carding Attack Works
A carding attack typically follows these steps:
- An attacker obtains a list of stolen credit card numbers, either from a criminal marketplace or by compromising a website or payment channel. Their quality is often unknown.
- The attacker deploys a bot to perform small purchases on multiple payment sites. Each attempt tests a card number against a merchant’s payment processes to identify valid card details.
- Credit card validation is attempted thousands of times until it yields validated credit card details.
- Successful card numbers are organized into a separate list and used for other criminal activity, or sold to organized crime rings.
- Carding fraud often goes undetected by the cardholder until it is too late when their funds are spent or transferred without their consent.
Attack Example: Carding Gift Cards
Hackers designed a malicious bot named GiftGhostBot to hack gift card balances. Nearly 1,000 eCommerce websites fell victim to this attack.
Criminals used this bot to enumerate through possible gift card account numbers, and automatically request the balance account of each card number. When a card balance was identified, instead of the usual error or zero, this meant the gift card number had real money associated with it. The crooks then used the validated gift card numbers to make purchases.
This is a card cracking or token cracking attack. For a cyber thief, the beauty of stealing money from gift cards is that it is typically anonymous and untraceable once stolen.
Detecting Card Fraud
Here are several pays payment websites can detect that carding bots are accessing their sites or other fraud techniques may be taking place:
- Unnaturally high shopping cart abandonment rates
- Low average shopping cart size
- An unnaturally high proportion of failed payment authorizations
- Disproportionate use of the payment step in the shopping cart
- Increased chargebacks
- Multiple failed payment authorizations from the same user, IP address, user agent, session, device ID or fingerprint
How to Protect Against Card Cracking Bots
The following techniques can help you safeguard your payment site against bad bots used in credit card cracking.
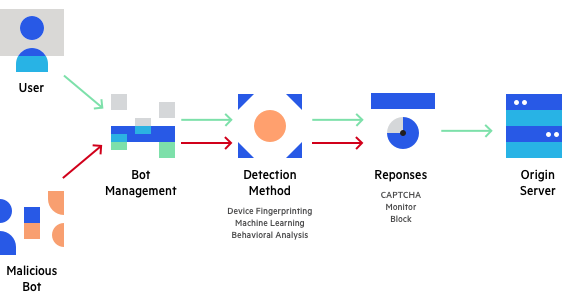
Bot management with Imperva
Device fingerprinting
Fingerprinting is done by combining the user’s browser and device to understand who or what is connecting to the service. Fraudsters or bots who are attempting credit card fraud need to make multiple attempts, and cannot change their device every time. They will need to switch browsers, clear their cache, use private or incognito mode, use virtual machines or device emulators, or use advanced fraud tools like FraudFox or MultiLogin.
Device fingerprinting can help identify browser and device parameters that remain the same between sessions, indicating the same entity is connecting again and again. Fingerprinting technologies can create a unique device, browser and cookie identifier, which, if shared by multiple logins, raises the suspicion that all those logins are part of a fraud attempt.
Browser Validation
Some malicious bots can pretend to be running a specific browser, and then cycle through user agents to avoid being detected. Browser validation involves validating that each user browser is really what it claims to be – that it has the expected JavaScript agent, is making calls in a way to be expected from that browser, and is operating in a way that is expected from human users.
Machine Learning Behavior Analysis
Real users visiting a payment website exhibit typical behavior patterns. Bots will typically behave very differently from this pattern, but in ways you cannot always define or identify in advance. You can use behavioral analysis technology to analyze user behavior and detect anomalies – users or specific transactions that are anomalous or suspicious. This can help identify bad blots and prevent cracking attempts.
As part of behavioral analysis, try to analyze as much data as possible, including URLs accessed, site engagement metrics, mouse movements and mobile swipe behavior.
Reputation Analysis
There are many known software bots with predictable technical and behavioral patterns or originating IPs. Having access to a database of known bot patterns can help you identify bots accessing your website. Traffic that may appear at first glance to be a real user, can be easily identified by cross-referencing it with known fingerprints of bad bots.
Progressive Challenges
When your systems suspect a user is a bot, you should have a progressive mechanism for “challenging” the user to test if they are a bot or not. Progressive testing means that you try the least intrusive method first, to minimize disruption to real users.
Here are several challenges you can use:
- Cookie challenge – transparent to a real user
- JavaScript challenge – slightly slows down user experience
- Captcha – most disruptive
Additional Security Measures
Beyond the above techniques, which allow you to directly validate if traffic originates from a real user or a bot, use the measures below to strengthen your security perimeter against cracking bots.
Multi-factor authentication
eCommerce sites can require users to sign in with something they know (for example, a password) and something they have (for example, a mobile phone). While this does not prevent cracking, it makes it more difficult for criminals to create large numbers of fake accounts, and renders it almost impossible for them to take over existing accounts.
API security
eCommerce sites often use credit card APIs, such as those offered by PayPal or Square, to facilitate transactions. These APIs can be vulnerable to attacks, such as JavaScript injection or the rerouting of data, if not incorporated with the appropriate security. To protect against many of these attacks, eCommerce sites can use a combination of Transport Layer Security (TLS) encryption and strong authentication and authorization mechanisms, like those offered by OAuth and OpenID.
Imperva Bot Management
Imperva’s Bot Management solution can protect against credit card cracking bots by using all the security measures covered above, letting you identify bad bots with minimal disruption to real user traffic:
- Device fingerprinting
- Browser validation
- Behavioral analysis
- Reputation analysis
- Progressive challenges
In addition, Imperva covers the additional security measures that complement a defensive bot strategy. It offers multi-factor authentication and API security – ensuring only desired traffic can access your API endpoint and blocks exploits of vulnerabilities.
Beyond bot protection, Imperva provides multi-layered protection to make sure websites and applications are available, easily accessible and safe, including:
- DDoS Protection—maintain uptime in all situations. Prevent any type of DDoS attack, of any size, from preventing access to your website and network infrastructure.
- CDN—enhance website performance and reduce bandwidth costs with a CDN designed for developers. Cache static resources at the edge while accelerating APIs and dynamic websites.
- WAF—cloud-based solution permits legitimate traffic and prevents bad traffic, safeguarding applications at the edge. Gateway WAF keeps applications and APIs inside your network safe.
- Account Takeover Protection—uses an intent-based detection process to identify and defends against attempts to take over users’ accounts for malicious purposes.
- RASP—keep your applications safe from within against known and zero‑day attacks. Fast and accurate protection with no signature or learning mode.