What is a botnet?
Occasionally referred to as a “zombie army,” a botnet is a group of hijacked Internet-connected devices, each injected with malware used to control it from a remote location without the knowledge of the device’s rightful owner. From the point of view of hackers, these botnet devices are computing resources that can be used for any type of malicious purposes—most commonly for spam or DDoS attacks.
An individual botnet device can be simultaneously compromised by several perpetrators, each using it for a different type of attack and often at the same time. For instance, a malware-infected personal computer could be ordered to rapidly access a website as part of a larger DDoS attack. At the same time it could also be performing vulnerability scans, with its owner browsing the web—unaware of both occurrences.
“We have a Botnet army ready to take down your site. You have 48 hours to pay us 1200$. Merry Xmas!” – DDoS ransom note
What is a DDoS attack?
DDoS is an acronym for distributed denial of service. A DDoS attack is a malicious attempt to make a server or a network resource unavailable to users. It is achieved by saturating a service, which results in its temporary suspension or interruption.
A Denial of Service (DoS) attack involves a single machine used to either target a software vulnerability or flood a targeted resource with packets, requests or queries. A DDoS attack, however, uses multiple connected devices—often executed by botnets or, on occasion, by individuals who have coordinated their activity.
DDoS attacks can be divided into two general categories:
1. Application layer DDoS attack types include HTTP floods, slow attacks (Slowloris, RUDY), zero-day assaults, and those targeting vulnerabilities in operation systems, web applications and communication protocols.
Comprised of seemingly legitimate and innocent requests, their magnitude usually being measured in requests per second (RPS), the goal of the attacks is to overwhelm a target application with requests. This causes high CPU and memory usage that eventually hangs or crashes the application.
2. Network layer DDoS attack types include UDP floods, SYN floods, NTP amplification, DNS amplification, SSDP amplification, IP fragmentation and more.
These are high-capacity barrages, measured in gigabits per second (Gbps) or packets per second (PPS). They’re almost always executed by botnets, with a goal of consuming the target’s upstream bandwidth, resulting in network saturation.
It should be noted that DDoS attacks can also target supporting infrastructures and services—most commonly the target’s DNS servers. These can be over-encumbered with a flood of fabricated DNS requests, originating from botnet devices.
DDoS botnet and botnet tools
The originator of a botnet is commonly referred to as a “bot herder,” or “botmaster.” This individual controls the botnet remotely, often through intermediate machines known as the command and control (C&C, or C2) servers.
To communicate with a C&C server, the botmaster uses various hidden channels, including seemingly innocuous protocols like IRC and HTTP websites, as well as popular services like Twitter, Facebook and even Reddit.
Botnet servers are able to communicate and cooperate with other botnet servers, effectively creating a P2P network controlled by a single or multiple botmasters. This means that any given botnet DDoS attack may have multiple origins, or be controlled by multiple individuals—sometimes working in a coordinated manner, other times operating independently.
Botnets-for-hire are available from various sources, their services often being auctioned and traded among attackers. Online marketplaces have even sprung up—these are commercial entities trading in huge numbers of malware-infected PCs. They can be rented and used for DDoS or other attacks (e.g., brute force).
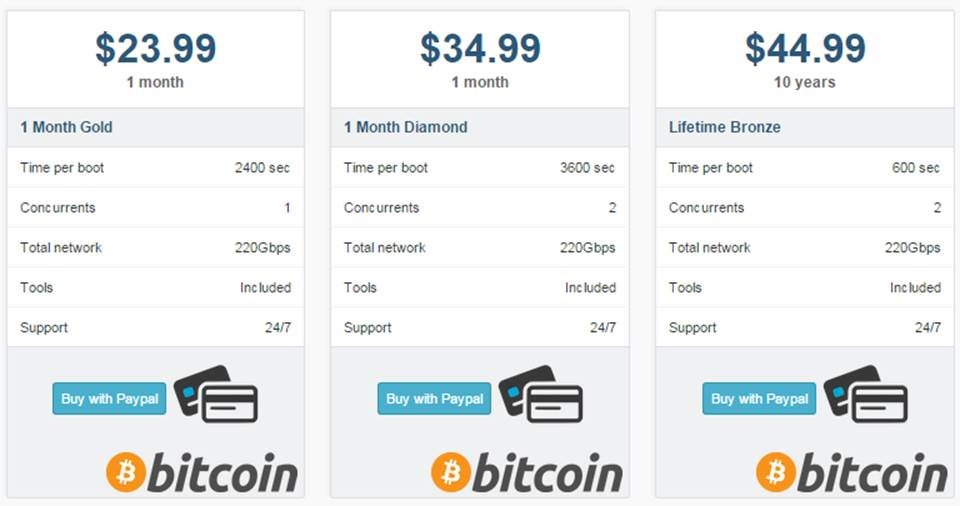 Typical DDoS stresser price list
Typical DDoS stresser price list
These platforms, often hiding behind the ambiguous service definition of stressers, or booters, sell DDoS-as-a-service. They provide their clients with a richly-featured toolkit, as well as a distribution network, so as to execute their attacks on call.
Now armed with a rented botnet, DDoS attacks have become a viable (if criminal) and cost-effective option for anyone looking to take out a website or disturb communication of home and office networks. This results in a number of attack scenarios, ranging from shady businesses using DDoS to gain a competitive advantage to assaults in which DDoS becomes a tool of vandalism, revenge or simply a way to get some attention.
Full-service DDoS attacks are available for as little as $5 per hour, and the interested party can easily stretch their hour with a monthly plan that averages $38. Within the cybercrime ecosystem, botnet DDoS attacks are a mainstream commodity; prices continually drop, while efficacy and sophistication is constantly on the rise.
Known botnets
Botnets are typically named after malware kits used in their creation. However, since botnet herders operate in anonymity, not all such kits are identifiable. Some of the most commonly used DDoS botnets are:
Nitol / IMDDOS / Avzhan / ChinaZ
This is an evolving DDoS botnet family that periodically morphs. It mostly operates in China. Once installed, its malware usually connects to the botnet’s C&C server using a TCP socket and then sends performance information from the victim’s machine.
Microsoft security researchers discovered in 2012 that Nitol-infected PCs were being sold in China on a mass scale; each device had a counterfeit Windows OS installed. Three years later, an Imperva report showed Nitol to be the most widely-spread botnet, infected machines accounting for 59.2 percent of all attacking botnet IPs.
MrBlack
Also known as Trojan.Linux.Spike.A, this malware targets the Linux platform, but is also available for various architectures and platforms (most commonly SOHO routers). It contacts a remote server, sending system information. Moreover, it receives control commands to perform different types of DDoS attacks against a given target, download a file and execute it, and then terminate a process.
In May 2015 a large-scale router-based, MrBlack botnet revealed itself, after taking part in mass-scale attacks against Imperva clients.
Cyclone
This is DDoS malware created in the U.S. It’s IRC-based and its C&C details are obfuscated. It’s known to kill off other bots on an infected host, in addition to stealing FTP credentials from Filezilla. Attacks include multiple HTTP floods, SlowLoris (though not slow), and ARME (Apache remote memory exhaustion).
Pushdo / Cutwail
Founded around 2007, Cutwail is a botnet mostly involved in sending spam e-mails. The bot typically infects computers running Microsoft Windows by way of a Trojan component called Pushdo.
Early in 2010 the botnetʼs activities were slightly altered when it was used in DDoS attacks against 300 major sites—including the CIA, FBI, Twitter and PayPal.
A 2015 report showed the Pushdo botnet affecting computer users in over 50 different countries—mainly India, Indonesia, Turkey and Vietnam.
Mitigating botnet DDoS attacks with Imperva
To protect against all DDoS attack types and with no additional software nor hardware installation, in a matter of minutes websites can benefit from Imperva’s comprehensive, cloud-based botnet DDoS protection service.
Network Layer Attacks
In the event of a network layer attack, Imperva provides dynamic resource overprovisioning—offering nearly limitless, on-call scalability. Additionally, Imperva’s reverse proxy helps mask original service IPs—a first line of protection against direct-to-IP attacks.
In an event where target IPs are already known, and the masking effect is insufficient, Imperva can enforce routing policies using BGP announcements. These ensure that all incoming traffic travels through Imperva scrubbing centers first, where it undergoes deep packet inspection.

Imperva mitigates a 250GBps DDoS attack—one of Internet’s largest.
Only then is clean traffic permitted to reach the origin via a secure, two-way GRE tunnel.
>> Learn more about Imperva’s Infrastructure DDoS Protection
During the mitigation process, the Imperva security system continually documents attacking IP addresses and assault patterns.
In real-time, this data is transmitted to Imperva’s DDoS threat database, so as to benefit all of our service users. This further enables a rapid response to emerging threats while minimizing risks posed by botnet IPs (and IP ranges) that were readily identified in previous attacks against Imperva clients.
Application Layer Attacks
Having the ability to sort DDoS bots from regular human visitors, Imperva’s proprietary security algorithms automatically detect any application layer offensive.
Here, bots are immediately identified using a combination of signature-based and behavior-based heuristics. Security challenges are employed behind the scenes to finalize the transparent profiling process.
As it is with network layer assaults, attacker information is added to Imperva’s communal DDoS threat database. Each mitigated attack adds to our system’s overall resilience, automatically improving it with each intrusion attempt.
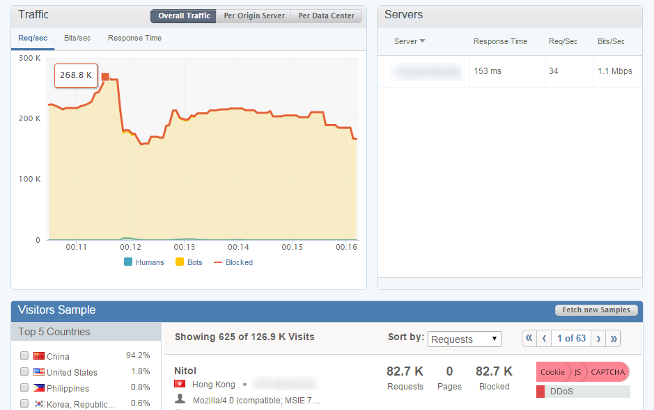
Imperva mitigates a 268K RPS HTTP flood DDoS attack.
>>Learn more about Imperva’s Website DDoS Protection
DNS-Targeted Attacks
Webmasters can set Imperva as their authoritative domain name server, while DNS zone file management remains independent of the Imperva cloud network.
With this service in place, all inbound DNS queries first reach Imperva, where malicious requests are automatically filtered out. Only legitimate ones are allowed to pass through, enabling smooth traffic flow at all times.
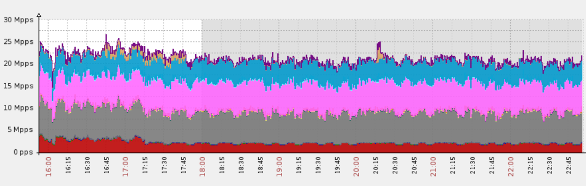
Imperva mitigates a massive DNS flood, peaking at over 25 million packets per second
>> Learn more about Imperva’s Name Server DDoS Protection













