What Is an Insider Threat
An insider threat is a security risk that originates from within the targeted organization. It typically involves a current or former employee or business associate who has access to sensitive information or privileged accounts within the network of an organization, and who misuses this access.
Traditional security measures tend to focus on external threats and are not always capable of identifying an internal threat emanating from inside the organization.
Types of insider threats include:
- Malicious insider—also known as a Turncloak, someone who maliciously and intentionally abuses legitimate credentials, typically to steal information for financial or personal incentives. For example, an individual who holds a grudge against a former employer, or an opportunistic employee who sells secret information to a competitor. Turncloaks have an advantage over other attackers because they are familiar with the security policies and procedures of an organization, as well as its vulnerabilities.
- Careless insider—an innocent pawn who unknowingly exposes the system to outside threats. This is the most common type of insider threat, resulting from mistakes, such as leaving a device exposed or falling victim to a scam. For example, an employee who intends no harm may click on an insecure link, infecting the system with malware.
- A mole—an imposter who is technically an outsider but has managed to gain insider access to a privileged network. This is someone from outside the organization who poses as an employee or partner.
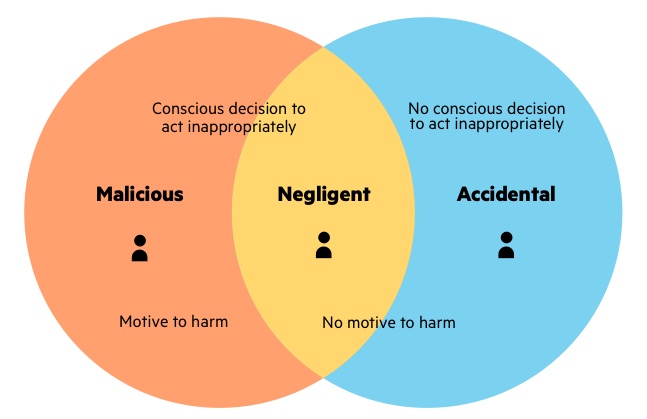
Three types of risky behavior explained
Malicious Insider Threat Indicators
Anomalous activity at the network level could indicate an inside threat. Likewise, if an employee appears to be dissatisfied or holds a grudge, or if an employee starts to take on more tasks with excessive enthusiasm, this could be an indication of foul play. Trackable insider threat indicators include:
- Activity at unusual times—signing in to the network at 3 am
- The volume of traffic—transferring too much data via the network
- The type of activity—accessing unusual resources
How To Protect Against an Insider Attack: Best Practices
You can take the following steps to help reduce the risk of insider threats:
- Protect critical assets—these can be physical or logical, including systems, technology, facilities, and people. Intellectual property, including customer data for vendors, proprietary software, schematics, and internal manufacturing processes, are also critical assets. Form a comprehensive understanding of your critical assets. Ask questions such as: What critical assets do we possess? Can we prioritize our assets? And, What do we understand about the current state of each asset?
- Enforce policies—clearly document organizational policies so you can enforce them and prevent misunderstandings. Everyone in the organization should be familiar with security procedures and should understand their rights in relation to intellectual property (IP) so they don’t share privileged content that they have created.
- Increase visibility—deploy solutions to keep track of employee actions and correlate information from multiple data sources. For example, you can use deception technology to lure a malicious insider or imposter and gain visibility into their actions.
- Promote culture changes—ensuring security is not only about know-how but also about attitudes and beliefs. To combat negligence and address the drivers of malicious behavior, you should educate your employees regarding security issues and work to improve employee satisfaction.
Insider Threat Detection Solutions
Insider threats can be harder to identify or prevent than outside attacks, and they are invisible to traditional security solutions like firewalls and intrusion detection systems, which focus on external threats. If an attacker exploits an authorized login, the security mechanisms in place may not identify the abnormal behavior. Moreover, malicious insiders can more easily avoid detection if they are familiar with the security measures of an organization.
To protect all your assets, you should diversify your insider threat detection strategy, instead of relying on a single solution. An effective insider threat detection system combines several tools to not only monitor insider behavior, but also filter through the large number of alerts and eliminate false positives.
Tools like Machine Learning (ML) applications can help analyze the data stream and prioritize the most relevant alerts. You can use digital forensics and analytics tools like User and Event Behavior Analytics (UEBA) to help detect, analyze, and alert the security team to any potential insider threats. User behavior analytics can establish a baseline for normal data access activity, while database activity monitoring can help identify policy violations.
How Imperva Protects Against Insider Threats
Imperva recognizes that user behavior analysis is key to protecting against insider threats, but is not enough. We provide a stack of solutions that not only monitors how users move through the network, but also protects assets on a data level, ensuring that whatever a malicious insider touches, you are in control.
Imperva’s industry-leading data security solution protects your data wherever it lives—on premises, in the cloud and in hybrid environments. It also provides security and IT teams with full visibility into how the data is being accessed, used, and moved around the organization.
Our comprehensive approach relies on multiple layers of protection, including:
- Database firewall—blocks SQL injection and other threats, while evaluating for known vulnerabilities.
- User rights management—monitors data access and activities of privileged users to identify excessive, inappropriate, and unused privileges.
- Data masking and encryption—obfuscate sensitive data so it would be useless to the bad actor, even if somehow extracted.
- Data loss prevention (DLP)—inspects data in motion, at rest on servers, in cloud storage, or on endpoint devices.
- User behavior analytics—establishes baselines of data access behavior, uses machine learning to detect and alert on abnormal and potentially risky activity.
- Data discovery and data classification—reveals the location, volume, and context of data on-premises and in the cloud.
- Database activity monitoring—monitors relational databases, data warehouses, big data and mainframes to generate real-time alerts on policy violations.
- Alert prioritization—Imperva uses AI and machine learning technology to look across the stream of security events and prioritize the ones that matter most.