What is Directory Traversal?
Directory traversal, also known as path traversal or directory climbing, is a vulnerability in a web application server caused by a HTTP exploit.
The exploit allows an attacker to access restricted directories, execute commands, and view data outside of the web root folder where application content is stored.
By manipulating input parameters or file paths, an attacker can navigate through the file system and gain unauthorized access to sensitive files or directories.
How Does Directory Traversal Work?
Directory traversal attacks manipulate variables that reference file paths within web applications. The attacker modifies the path variables to move upwards in the directory structure or to traverse to different directories. This is typically done using specific sequences like `../` or `..\` in Unix and Windows systems, respectively.
An attacker might use the sequences in a URL or input field in an attempt to trick the server into returning a file from outside of the document’s root directory.
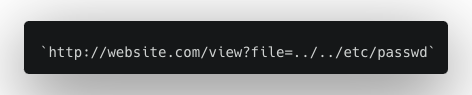
Example:

Requesting a URL like the example above attempts to have the server return a sensitive system file.
Attacks stemming from directory traversal can be damaging if they’re used to display system files or download sensitive information. It can allow an attacker to view, edit, or execute arbitrary files on the server’s file system, leading to a potential compromise of the server.
What’s the Difference Between Local File Inclusion and Directory Traversal?
Local File Inclusion (LFI) and Directory Traversal are both security vulnerabilities exploited to gain unauthorized access to files on a server, but they differ in operation and potential impact.
Local File Inclusion (LFI) allows an attacker to include a file, usually exploiting a script on the server, and execute it from a local directory within the server. This vulnerability occurs when a web application uses unsanitized user input to construct a file path for execution. LFI allows the execution of scripts, which could potentially lead to a full system compromise.
Directory Traversal attacks, or path traversal, aim to access files in a directory that the attacker should not have access to by manipulating variables that reference file paths. The attacker doesn’t necessarily need to execute a file, as the main goal is to read sensitive files to gather data. This type of attack is often used to gather information to inform future attacks.
While both security vulnerabilities exploit file inclusion mechanisms of web applications, LFI enables script execution, while directory traversal is typically used for unauthorized data access.
Example of a Directory Traversal Attack
In this example, imagine a simple web application that allows users to view an image file. The application might use a query parameter to determine which file to display. For example, a URL might look like `http://website.com/view?file=logo.png`. The server-side code handling this might look something like this in PHP:

Under normal circumstances, this would work fine. The `file` parameter defines which file to display to the user, so `file=logo.png` would show the logo image.
However, an attacker could manipulate the `file` parameter to move up directory levels and access restricted files. By using the directory traversal sequence `../`, they can move up one directory.
If the attacker requests the following URL, they could view the contents of a sensitive system file containing user account information.
The manipulated server-side code would look like this:

This results in the server navigating to:
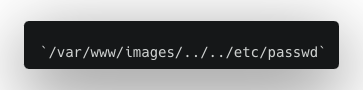
After resolving the relative directory `../`, it points to
This effectively allows the attacker to view this system file.
To prevent such an attack, developers must sanitize all user inputs and restrict the type of input that can be processed. By ensuring that all inputs follow a certain format — such as checking that the input is a valid filename and does not contain directory traversal sequences — these vulnerabilities can be effectively neutralized.
What are the Risks of Directory Traversal?
Directory traversal poses three significant threats to the security and integrity of web servers and applications:
- Directory traversal can lead to unauthorized access of sensitive information stored in files outside of the web root directory. This could include: system files, configuration files, or even user data. The unauthorized access of confidential data is a direct breach of privacy and can lead to information theft.
- Attackers can read and also modify or delete critical files, causing serious system malfunctions or service disruptions. This can lead to significant downtime, loss of productivity, and even financial loss.
- Successful directory traversal attacks can provide attackers with the ability to carry out damaging attacks. For instance, gaining access to certain system files can provide valuable information about the server’s structure, configuration, and the security measures that are in place. Taken together, this is information that can be used to construct more sophisticated attacks in the future.
Directory traversal is a serious security risk that can lead to the compromise of privacy, integrity, and availability of web servers and applications.
Tools Used by Attackers to Locate Directory Traversal Vulnerabilities
Threat actors use a variety of tools to identify directory traversal vulnerabilities in web servers and applications. Here are some of the most commonly used:
- Burp Suite: This is a comprehensive web application security testing platform. It includes a variety of tools, including a scanner that can automatically detect directory traversal and other common vulnerabilities. Its Intruder tool can also be used to test for traversal vulnerabilities manually.
- OWASP ZAP (Zed Attack Proxy): This is a free, open-source web application security scanner developed by the Open Web Application Security Project (OWASP). It can identify a wide range of vulnerabilities, including directory traversal.
- Nikto: A server scanner that checks servers for dangerous files, outdated server software, and other problems. It can also detect directory traversal vulnerabilities.
- DotDotPwn: This tool, as its name suggests, is specifically designed to test for directory traversal vulnerabilities. It operates by sending specially crafted requests to the server and analyzing the responses.
- Metasploit: This is a penetration testing framework that contains modules for testing a wide range of vulnerabilities, including directory traversal.
- DirBuster: A tool from OWASP that aims to find hidden directories and files from servers. It can also help in finding directory traversal endpoints.
The use of these tools underscores the importance of regular security testing and vulnerability scanning in web applications. However, it is worth noting that these tools can also be misused by threat actors, which reinforces the need for strong security measures and practices.
Preventing Directory Traversal Attacks
There are several strategies an organization can use to control and validate user input.
- Input validation: This is the first line of defense against directory traversal attacks. Ensure all user inputs are validated and sanitized before they are processed. Reject any suspicious input containing special characters like `../` or `..\` used in directory traversal.
- Use of allow lists: Instead of blocking known bad inputs (a blocklist), it’s more effective allow known, good inputs (an allow list). For instance, if your application needs to access specific files, list those files and only allow access to them.
- Avoid using user input for file operations: If possible, avoid using user input to access files. If you must, ensure the input is strongly validated and does not contain directory traversal sequences.
- Use of built-in functions to normalize paths: Many programming languages offer functions that can normalize paths and remove any directory traversal sequences. For instance, in PHP, you can use the `realpath()` function, and with JavaScript, the `getCanonicalPath()` method can be used.
- Least privilege principle: Ensure applications run with the least privileges necessary. This can limit a potential directory traversal attack as the attacker can only gain access to limited resources.
- Regular security testing: Test applications regularly for security vulnerabilities. Tools like Burp Suite, OWASP ZAP, Nikto, DotDotPwn, Metasploit, and DirBuster can help identify potential directory traversal vulnerabilities.
The key to preventing directory traversal attacks lies in strong input validation, prudent coding practices, and regular security testing.
How to Mitigate Directory Traversal Attacks
Mitigating the effects of a directory traversal attack involves a series of immediate and strategic actions.
- Incident response: As soon as a breach is detected, follow an established incident response (IR) plan. This usually includes isolating the affected system to prevent further compromise, conducting a thorough investigation to understand the extent of the breach, and notifying affected parties and regulatory bodies if necessary.
- Patch and update systems: Ensure that systems and applications are using the latest, patched versions. Developers and vendors often release updates that fix security vulnerabilities, including directory traversal. Regular patching can help mitigate the damage from known vulnerabilities.
- Deploy a Web Application Firewall (WAF): A WAF can provide an extra layer of security by detecting and preventing attacks, including directory traversal attacks. It works by examining HTTP traffic and identifying patterns or sequences that match known attack vectors.
- Regular audits and vulnerability assessments: Regularly conducting security audits and vulnerability assessments can help you identify potential weaknesses in your systems and applications.
- Educate and train your team: The development and IT team should be familiar with the concept of directory traversal attacks and other common web application vulnerabilities. They should be trained in secure coding practices and kept up-to-date on the latest threats and mitigation strategies.
- Backup and recovery plan: Putting a robust backup and recovery plan in place can help an organization recover quickly in the event of a serious attack. Regularly back up all important data and ensure that systems can be restored after an incident occurs.
How Imperva WAF Can Stop Directory Traversal Attacks
Imperva Web Application Firewall (WAF) offers the industry’s leading web application security firewall, providing enterprise-class protection against the most sophisticated security threats.
Whether your websites and applications are hosted in the public cloud or on-premises, Imperva ensures critical assets are always protected against any type of application-layer vulnerability or attack, such as a directory traversal.
Imperva WAF delivers protection in several ways:
- Traffic inspection: Imperva WAF continuously monitors and examines HTTP traffic, looking for patterns or sequences that match known attack vectors.
- Security rules: Imperva WAF offers a set of out-of-the-box rules that can help prevent a range of threats. The product also allows for the implementation of custom security rules that can be specifically tailored to detect and block directory traversal attempts.
- Signature-based detection: Imperva WAF can recognize patterns of malicious activity, including those used in directory traversal attacks. Immediate detection helps to block attacks before they can cause any harm.
- Machine learning: Imperva WAF uses machine learning algorithms that aid in detecting anomalous behavior and potential attacks. This includes uncommon request patterns that might indicate a directory traversal attack.
- Location-based blocking: Block or limit traffic from specific locations, especially f directory traversal attacks are repeatedly originating from a particular location, you can effectively block all requests from that region.